The Nova Swan Theory
Introduction to one of my analytical framework
Here is a “formal” introduction to the concept I came to widely use over the last few years. The aim of this piece is to serve as an introduction to many concepts that are used and applied daily at many levels at a global level, while long it is not as encompassing as I would like.
One “intellectual” trick I picked from experience is “Grab what is useful, discard what isn’t”, the Nova Swan should be no different for you, use or apply what feels useful to you, and ignore what doesn’t. Build your own framework based on this, and create something entirely novel with time. Curiosity and necessity are the only limits.
Introduction
First to understand what is the Nova Swan (theory, hypothesis, whatever descriptive term you may prefer to use) a little context on the basis for the concept goes a long way. I modeled the Nova Swan on two very distinct in nature, similar in cascade effect potential.
The first was the Kessler Syndrome or Cascade. KS/C is the theory of one too many pieces of space technology, more often referred to as “space trash” being so numerous that there is an ever-increasing chance of planet-locking humanity by the sheer scope of destruction. A small object at a substantial velocity hits a satellite, and that satellite breaks into small pieces, those pieces flow out at significant speed, and this creates a catastrophic cascade effect encompassing basically all satellites.
The second concept used was a Near-Earth Super Nova. A NESN will not kill everyone on the planet instantly, theoretically, it won’t cause that much damage at first, but it will increase the ocean temperatures so fast that it will wipe out most of the oceanic ecosystem. Similar to the KS, this creates a global, catastrophic collapse of biological systems, referred to in complexity science as a “co-extinction cascade”. A nice concept to learn on your own, although mildly tainted by green narrative these days.
The entire concept wouldn’t exist without “the black swan”, and while I am aware of many other literary instances very similar to the black swan, I am fond of this one, it has the biggest and most potent memetic effect =).
The Nova Swan
The Nova Swan represents a new paradigm in catastrophic occurrences, surpassing the impact of traditional Black Swan events, it represents an unprecedented event that sends shockwaves through societal systems, dwarfing the consequences of its initiating event. One specific unique characteristic of the Nova Swan is its potential to be used as an objective implemental concept of Hybrid War, enabling entities to exploit an initial Black Swan to foment the birth of a Nova Swan. One of my main arguments for years is events that lead to a Black Swan can be engineered. The Black Swan itself is “unpredictable”, but the many dominos falling leading to a cascade of events isn’t.
One of its defining features is the unforeseen potential within the even, lying dormating, waiting to be harnessed. The initial event may seem ordinary or innocuous initially (as pneumonia spreading fast in China), but its true implications only become apparent as the cascade effect takes hold.
By understanding the stages of a Nova Swan and examining the theoretical possibilities, from how to gather, measure, track, and analyze data, you are able to see the hidden potential in non-linear events, but not limited to it, one is able to apply this framework/concept to all fields of human knowledge and endeavor and can understand the basis of my perspective on Hybrid Warfare, longer-term planning, and something that is a “sin” among many sciences “Probabilistic Manipulation”, or how powerful organizations could engineer and exploit such events, and by exploring all these intricate topics we can gain insights into the potential manipulation of societal systems, even at a civilizational scale. My goal is to provide an introductory, but somewhat comprehensive framework, starting from basic concepts and progressing toward more complex aspects.
As a side note, you can substitute organizations for any form of complex system. My focus here on organizations (non-state actors, elites, etc) is solely for…future reference.
To grasp the magnitude of a Nova Swan event, it is vital to comprehend the power of exponential growth. In many cases, the initial event serves as a trigger, propelling the system into a state of accelerating deterioration. The consequences of the event multiply rapidly, overwhelming existing structures and institutions. A mathematical analogy can aid in understanding this phenomenon.
Consider a simple exponential growth model where a quantity doubles over a fixed time interval. If we apply this concept to the stages of a Nova Swan, the initial event can be likened to the first doubling. However, the subsequent doubling occurs at an accelerated rate, leading to an exponential surge in impact. This exponential growth creates an unprecedented cascade of effects that is difficult to predict or contain within conventional frameworks.
Armed with a deeper understanding and applicability of many different analytical frameworks equipped with substantial resources one may leverage their understanding of system dynamics to both orchestrate or navigate the many stages of a Nova Swan event, providing fertile ground to implement rapid changes and push forward their desired agendas. Exploiting confusion and desperation that arise from such events you are able to leverage vulnerabilities and failures that emerge during the cascade, capitalizing on the resulting chaos to enact policies, acquire assets at reduced prices or consolidate control over critical sectors.
Economies, governments, and infrastructures exhibit nonlinear behavior, meaning small inputs can result in disproportionate outputs. This nonlinearity is an inherent characteristic of Nova Swan events, amplifying the consequences beyond the expectations derived from the initiating event. Different analytical methods can help you better understand and forecast the non-linear behavior and dynamics inside a “Nova Swan cascade”, mathematical models often play a crucial role in enlighting both its effects and the potential pressure points for manipulation of such complex events.
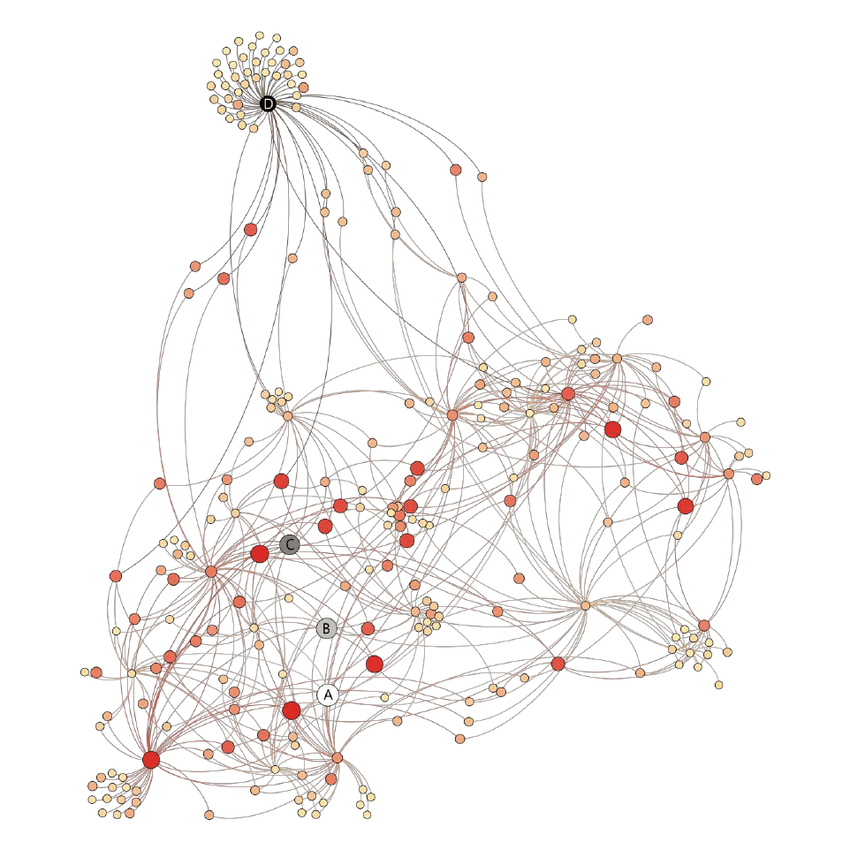
Network theory can help understand the interdependencies and vulnerabilities within the Nova Swan, especially with regard to societal systems. By identifying critical nodes and potential influential actors, one could target specific points to trigger or amplify the cascade effect, thereby maximizing their influence and making it easier to both achieve their end goal and grow chaos, as an obfuscation tool. Game theory can enable you to examine all potential strategic interactions among various “moving parts” in the Nova Swan event from a geopolitical perspective.
One should never interpret or see an event, as a singular event in a linear, two-dimensional line, but a point is a non-linear network of relationships and effects.
Given the inherently chaotic nature of the event, encompassing and being modeled after complex events and complex systems, complexity theory is one of the best subjects to delve into to understand and being able to characterize the interconnections, feedback loops, and nonlinearity of the Nova Swan, or complex system for that matter. Exploring how small changes in initial conditions or system parameters can lead to profound and unpredictable outcomes can lead you to many insights through events or life but in the context of the Nova Swan, it aids us in identifying patterns, emergent behavior, and interdependencies within the cascade effects.
Aforementioned above, nonlinear effects lies at the heart of a Nova Swan event, defining its potential to transform its transformative nature and the exponential amplification of consequences, 3 concepts to keep in mind are :
Feedback loops - They play a crucial role in driving nonlinear effects in any type of complex system, from societies, and culture to our cellular biology. Feedback loops can both be positive or negative, both mitigating or enhancing the nonlinear effects of an event, in a simplistic level on a very complex topic, they act as gravity modifiers.
Tipping point - Nonlinear effects are often born out or through tipping points, which are critical thresholds within any system. Crossing these thresholds can trigger a sudden and significant shift in behavior or outcomes, outweighing the capacity of a system to handle drastic changes. Tipping points are applicable and present in every single facet of human life (and are a subfield of complexity science on its own)
Emergent properties - These properties emerge from the collective behavior of the individual components, resulting in these components interacting and forming complex patterns of behavior. This can lead to diverse and unexpected outcomes, from cascading failures, rapid system-wide changes, or the emergence of new organizational structures.
There is much more to it, but these concepts allied with the following ones are enough for you to spend considerable time learning them. Understanding nonlinear effects within complex systems is crucial for effectively utilizing the tools and techniques of probabilistic manipulation. This requires a deep understanding of how the system's behavior emerges from the interactions of its components and the ability to assess the potential consequences of manipulating certain variables or parameters. Ultimately, the understanding of nonlinear effects empowers individuals to navigate the intricacies of the system, anticipate emergent patterns, and execute probabilistic manipulation strategies with precision and effectiveness.
As I often said in the last 2 months, data is gold, and data collection is one of the most important and crucial tools to both understand the dynamics and identify leverage points. I will stick to a few “common variables” of our times in regard to the uses of these tools, otherwise, each section would be an entire page.
Surveillance and Monitoring - comprehensive surveillance and monitoring system to gather real-time data on mortality rates, cyber attack incidents, energy supply disruptions, and societal responses. This can involve monitoring official sources, news reports, social media platforms, dark web channels, and specialized intelligence networks. Automated data scraping tools and web crawlers may be employed to gather relevant information from publicly available sources.
Sensor Networks and IoT Devices - Sensor networks and Internet of Things (IoT) devices to collect data on vital parameters such as infection rates, energy consumption, and network traffic. This includes deploying IoT devices in healthcare facilities, critical infrastructure, and public spaces to capture real-time data. Sensor data can provide valuable insights into the spread of the virus, energy usage patterns, and potential vulnerabilities for cyber attacks.
Big Data Analytics and Machine Learning - Advanced data analytics techniques, such as big data analytics and machine learning algorithms, to process and analyze the collected datasets. These techniques enable the identification of patterns, correlations, and trends that may not be apparent through manual analysis. Algorithms such as clustering, classification, and anomaly detection can be applied to identify critical events, potential cyber-attack patterns, and emerging vulnerabilities.
- Anomaly Detection - Applying machine learning algorithms to detect unusual patterns, deviations, and anomalies in large datasets, enabling the identification of emerging risks or critical shifts.
Social Media Analysis - Social media analysis techniques to gather insights from user-generated content. Natural language processing algorithms, sentiment analysis, and social network analysis are employed to identify public sentiment, emerging trends, and potential vulnerabilities. This enables one to gauge public response, identify influential individuals or groups, and manipulate the information flow through targeted disinformation campaigns.
The last two were widely and exponentially used in the last 3 years in regards to the SARS-CoV-2 pandemic, especially the last one. It was one of the pillars of all and every single effort by every NGO and government alike to manipulate entire populations into accepting one of the most egregious decisions in modern human history. Arguably every step to be discussed from here on was implemented at different levels, to different degrees of success, but certainly became a map for “the next one”.
After gathering enough information via any of these methods or actively using data brokers to skip this step, both saving time and money, the next step is to identify critical decision points within the Nova Swan cascade of events, these key junctures present the opportunity to apply strategic intervention thus proportionating significant impact on the course of events.
Network analysis techniques are applied to ma; out the interconnectedness of the system and identify such critical nodes and edges within the network. By analyzing the dependencies and interdependencies among different entities, such as healthcare providers, government agencies, critical infrastructure operators, and supply chain networks, the manipulating entity can pinpoint decision points that have cascading effects on the overall system.
Exploitation of Systemic Vulnerabilities
All steps below assume there is a group of individuals, organizations, or entities effectively aiming to exploit such events, and I will write from that perspective. After all, as once an influential individual told me “Systems don’t magically manipulate themselves”.
This step involves understanding the inherent weaknesses, interdependencies, and leverage points within the system, and strategically exploiting them to achieve desired outcomes. The exploitation of systemic vulnerabilities requires a multifaceted approach that combines various techniques and tactics, there are no right or wrong, but different approaches, tailoring each set of tools to the task at hand with an end goal in mind.
Leveraging Interdependencies - By targeting specific decision points that have ripple effects across multiple interconnected systems, they can exploit vulnerabilities and trigger cascading effects. For example, if the energy supply chain is already strained due to the Nova Swan event, the entity may strategically disrupt critical nodes within the supply chain, exacerbating the energy shortage and causing widespread disruptions in other sectors. This can amplify the impact of the event and create a sense of chaos and vulnerability within the system.
Disinformation and Psychological Manipulation - Exploiting the power of information and perception, disinformation campaigns, and psychological manipulation tactics. The dissemination of misleading information sows confusion and exploits existing fears and anxieties within the population. By influencing public opinion, can create divisions, erode trust in institutions, and manipulate the decision-making processes of key individuals. Techniques such as social media manipulation, and targeted propaganda are employed to shape public narratives and distort reality to serve their agenda.
Cyber Attacks and System Breaches - Targeting healthcare systems, energy grids, communication networks, and other essential infrastructure to cause widespread chaos and amplify the impact of the Nova Swan event. Techniques such as ransomware attacks, distributed denial-of-service (DDoS) attacks, and supply chain compromises are utilized to exploit weaknesses in cybersecurity defenses and compromise the integrity and availability of critical systems.
Strategic Resource Manipulation - Identifying key resources that are essential for the functioning of the system and strategically manipulating their availability or distribution. For example, hoarding critical medical supplies, strategically controlling the distribution of food and water or manipulating the availability of energy resources. By creating artificial scarcity or manipulating access to vital resources, exerting control over the system, amplifying the vulnerabilities caused by the Nova Swan event, and furthering objectives.
Covert Influence and Strategic Alliances - A manipulating entity seeks to establish covert influence over key decision-makers, institutions, and influential individuals within the system. Employing tactics such as bribery, coercion, and strategic alliances to gain access to critical information, influence policy decisions, and shape the response to the event. By infiltrating key positions of power or manipulating existing power dynamics, they can steer the system towards outcomes that align with their objectives.
Economic Manipulation and Market Distortion - Recognizing the interconnectedness of economic systems, a manipulating entity exploits market vulnerabilities and engages in economic manipulation. They may engage in speculative activities, manipulate prices of essential goods, or create artificial shortages to destabilize the economy and further their influence. By exacerbating economic hardships and creating financial dependencies, they can manipulate decision-making processes and exert control over the system.
Supply Chain Disruption deserves this small addendum on its own.
Targeted Disruptions: Disrupting key supply chains, such as pharmaceuticals, medical equipment, or food, through cyber attacks, sabotage, or geopolitical strategies, leading to shortages and vulnerabilities.
Manipulation of Logistics: Disrupting transportation networks or logistics operations, causing delays, bottlenecks, or disruptions in the distribution of critical supplies.
At this point, this could be further broken down into another core of concepts that influence the probabilities, or tilt events and dynamics into a certain direction. Exerting covert influence on decision-making processes using subtle manipulation, strategic alliances, and covert action aimed at shaping the decision and actions of key figures.
Strategic Networking and Alliances - By strategically establishing networks and alliances with influential individuals, organizations, and decision-makers, one can leverage existing relationships or create new connections to gain access to decision-making circles, thus exerting indirect influence, shaping narratives, and manipulating from within. Bribery, lobbying, coercion, and blackmail are the most common tactics used to sway decisions in “your” favor. This is also, effectively, how the WEF works, in fact, almost every step describe here in retrospect is how they operate, with the exception of data-linked processes…for now.
Information Manipulation - Selectively present information, distort facts, and emphasize certain aspects while downplaying others to shape perceptions and influence the judgments of decision-makers. By controlling the narrative and framing the discourse, swaying opinions, and guiding decisions toward their desired outcomes. Techniques such as propaganda, misinformation campaigns, and strategic leaks of sensitive information are utilized to manipulate decision-making processes.
Psychological Manipulation - Employing psychological manipulation techniques to influence the mindset, emotions, and cognitive biases of decision-makers. Techniques such as persuasion, framing, and manipulation of cognitive heuristics are used to shape perceptions, create cognitive dissonance, and influence the choices made by decision-makers. By exploiting human vulnerabilities and biases, they can steer decisions toward outcomes that align with their objectives.
Exploitation of Psychological Vulnerabilities - Exploiting human emotions, such as fear, anxiety, and distrust, to manipulate behaviors and reactions. Through targeted psychological manipulation tactics, they intensify these emotions, leading to irrational decision-making, increased social fragmentation, and the breakdown of societal cohesion. This amplifies chaos and makes the population more susceptible to the influence and control of interested parties.
Covert Operations and Sabotage - In some cases, the manipulating entity may resort to covert operations and sabotage to undermine decision-making processes. This could involve actions such as espionage, sabotage of critical infrastructure, or spreading disinformation to discredit key decision-makers. By destabilizing the decision-making landscape, they can create chaos, erode trust, and manipulate the choices made by decision-makers. These covert actions aim to create an environment conducive to the manipulation entity's objectives.
Infiltration and Impersonation - The manipulating entity or organization may employ tactics such as infiltration and impersonation to gain direct access to decision-making processes. They may infiltrate organizations, committees, or advisory groups to influence the decision-making discussions and outcomes. By assuming false identities or posing as trusted individuals, they can sway decisions, manipulate agendas, and suppress dissenting voices.
Institutional Manipulation - Recognizing the influence of institutions in decision-making processes, one can exert pressure on institutions, compromise their integrity, or manipulate their processes to favor decisions that align with their objectives. This could involve co-opting key personnel, influencing policy formulation, or exploiting loopholes in governance frameworks. By manipulating institutions, they can shape the decision-making landscape and ensure decisions are conducive to their agenda.
Other broad tactics to achieve geostrategic interests.
Proxy Conflicts - Exploiting existing geopolitical tensions by fueling proxy conflicts, supporting insurgent groups, or exacerbating regional rivalries, leading to increased chaos and instability.
Hybrid Warfare Tactics - Blurring the lines between conventional warfare, cyber warfare, and information warfare to undermine infrastructure, sow discord, and amplify chaos in targeted regions.
Destabilization of Governments - Supporting or fueling dissent within governments, promoting political polarization, or funding opposition groups to create internal strife and amplify chaos.
I decided to not cover some subjects given how extensive and already complex this piece was, I plan to write other substacks within this subject, giving my perspectives, and building upon this framework, but overall, you may refer to this map as much as you need, and build your own, adding or removing what you see fit.
After reading this, it is important for you, the reader, to approach and apply this framework with a critical mindset and open curiosity, the Nova Swan theory, which emphasizes black swan events, complex systems, nonlinear dynamics, systemic vulnerabilities, decision-making processes, and many forms of data analysis provides a stepping stone for you to comprehend the complexities of contemporary events, their potential consequences, and how feasible it is to execute large scale manipulation.
Engage in further exploration, and embrace systems thinking approach, considering how interconnected complex systems are and their feedback loops. Analyze events from a holistic perspective, identifying patterns, emergent behavior, and interdependencies that contribute to the overall dynamics. Hone your analytical skills, such as data collection, analysis, and modeling techniques, and your critical thinking. Analyze real-world events and consider their nonlinear effects, attempting to find systemic vulnerabilities.
May this be the first step of many towards seeing how much of every facet of our contemporary existence is manipulated at every perceivable level one could think, and this may bring to light my instances on many subjects, persons, and “influencers” of all sorts and manners, and why I care little about politics.
If you chose to support my work, thank you !








Will be commenting more on this, but, once again - brilliant writing. I read quite a few substacks regularly...this is by far the best one.
In order to plan the initial black swan event in hopes of starting a cascade effect which you prefer you must base that plan on predictable human behaviors and reactions.
One error I’ve seen in prior black swan events was a miscalculation not in the plan or the collective social responses but in underestimating the intellect of outliers and underestimating the degree to which certain groups are “loyal” to particular leaders. There are a significant number of people that only merely “appear” to have political loyalties and preferences for certain leaders/figures. This is where those planning black swan events make an error. The subscribe too narrow a view of the social groups they mean to manipulate. Their own arrogance and vanity limits their ability to see that the outliers will always throw a monkey wrench in the results of black swan events.
Therefore to the degree that people can part ways with strict ideological stereotypes and cult like loyalties we would become collectively far more unpredictable and more difficult to manipulate. The more entrenched in group think the more susceptible we are to black swan events. The lesson - don’t be boxed in. Be a free thinker.